
Before we start with this Blogpost we take a short look back…
Nearly 10 years ago Symantec made the first steps into the MDM / MAM space with the acquisition of two companies.
2012 Symantec bought two different Mobile Device Management Companies: one was called Odyssey (Athena) and a second company called Nukona (AppCenter). The Odyssey Product was later integrated into the ITMS Console while the Nukona Product needs its own infrastructure (CentOS / RHEL + MySql as DB).
The Odyssey Product had an integration into Microsoft System Center Configuration Manager and mainly was a traditional MDM Product, while the Nukona Product was focused on MAM.
In 2016 first the Odyssey Product got EOL and later the Nukona Product (Appcenter) was EOL´d. That marked the end of Symantec in the MDM space.
Symantec is now entering the MDM space again with its upcoming ITMS 8.6 RU2 release. This time they decided to build the product on an open source platform called MicroMDM instead of buying a company and integrating the product.
With this release Symantec will potentially take the necessary steps to transform from a traditional Management Solution to a Modern Unified Endpoint Management (UEM) Solution combining both into a single Product.
Introduction
In this Blogpost you will find some information about MDM vs. traditional Management and my personal view. Please keep in mind that this Blogpost does not represent a commitment from Broadcom / Symantec.
Why is it important to have MDM management?
In the future MDM will become more important for most companies. For example Microsoft recently released KB5005101 which enables over 1400 new MDM policies. With them, you can configure policies that Group Policies also support. These new MDM policies include administrative template (ADMX) policies, such as App Compat, Event Forwarding, Servicing, and Task Scheduler.
Managing devices the traditional and the modern way – the differences?
When managing devices using MDM, no Management Agent is needed. Devices will be enrolled into an MDM Server using an enrolment URL that allows management of the devices and the vendor provides the management APIs. For example: Lock Device, Wipe Device, Wifi Configuration, E-mail Configuration and many more, depending on the Platform you are to managing. Therefore different management functions are available from different vendors.
Microsoft provides CSPs (Configuration Service Provider) to allow management settings through MDM. APIs are available for all MDM vendors and so all of them can use them in their products.
I expect that managing devices through MDM is the future and the vendors (MS, Apple, Google….) will provide more and more MDM features.
Nevertheless most enterprise companies still rely on traditional management capabilites because some MDM capabilities aren´t that granual to configure or still missing some important capabilities.
Possibilities with full-blown Management Agent vs. MDM enrolled?
Currently the situation is that on the Windows Platform you still have more and granular options when managing devices using a full-blown Agent. MDM doesn´t offer the same functionality yet when you are trying to compare the options between full-blown Agent and MDM enrolled but Microsoft opens more and more management capabilities using MDM. So managing Devices this way will get more and more interesting and important. In other words, it absolutely make sense to have both possiblities.
On other Platforms like iOS and Android managing devices using MDM / MAM is the way to go…
Keep in mind that you can´t enroll your devices into multiple MDM products at the same time. When managing devices using MDM you have to make a decsion for a single MDM Vendor.
When managing devices using a full-blown agent you can install the agent from vendor A and vendor B and manage the device with both products (mostly this doesn´t make sense). Moving away from management vendor A to vendor B is in most cases much simpler than to change the MDM / MAM solution in terms of coexistence.
Advantages combining Full-blown Management Agent and MDM capabilities?
The advantages of combining managing devices with a full-blown agent + managing devices using MDM is that customers had a very rich set of features and functions to manage their devices.
The current state in ITMS 8.6 RU1 – Technical Preview
In ITMS 8.6 RU1 Symantec offers a Release Preview for the MacOS MDM functionality but it´s only available to selected customers and partners by invitation. Customers or partners who are interested in the technical preview can contact Mike Gruber by sending a personal message to me via my post in the online community.
Prerequisits for ITMS 8.6 RU1 – Technical Preview
A new Site Server Role is introduced for the MDM Server that can be an Ubuntu or Redhat Server.
The Linux ITMS Agent needs to be installed on the Ubuntu / Redhat Server.

Installation of an „Altiris MDM Agent“ on Ubuntu or Redhat MDM Site Server is necsessary (similar process like an NBS, Package and/or Task Server) and this MDM Server will act as proxy for MDM communication.

The MDM Site Server can be hosted in the corporate Network, DMZ or in the cloud and can be fully managed from the SMP Server user interface.
As with any other MDM System, an Apple Push Notification Service (APNs) certificate needs to be issued for managing Apple Devices.
ITMS 8.6 RU1 MacOS – Technical Preview a High Level Overview
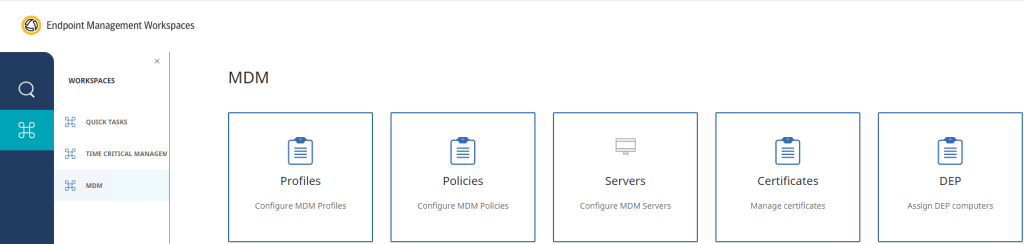
You can access and configure the MDM capabilities in the Workspaces.
(ITMS Console -> Home -> Endpoint Management Workspaces).
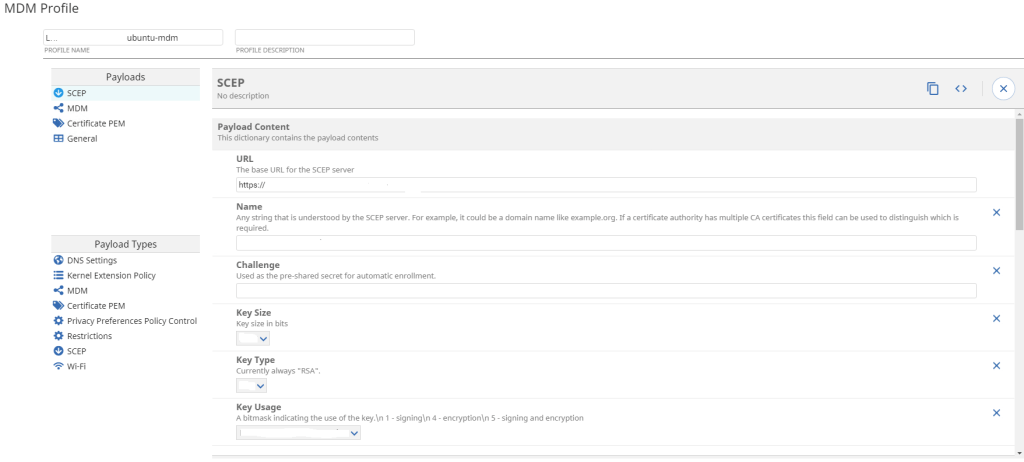
Before you are able to manage MacOS Devices, you need to configure an enrollment profile and assign it to your „Altiris MDM Site Server“. You need to add a couple of payload types to your enrollment profile to make it work correctly. In 8.6 RU1 the following payloads are supported: MDM, System Extension Policy, Privacy Preference Policy Control (PPPC/TCC), WiFi, Restrictions, SCEP, Certificate PEM and DNS Settings.
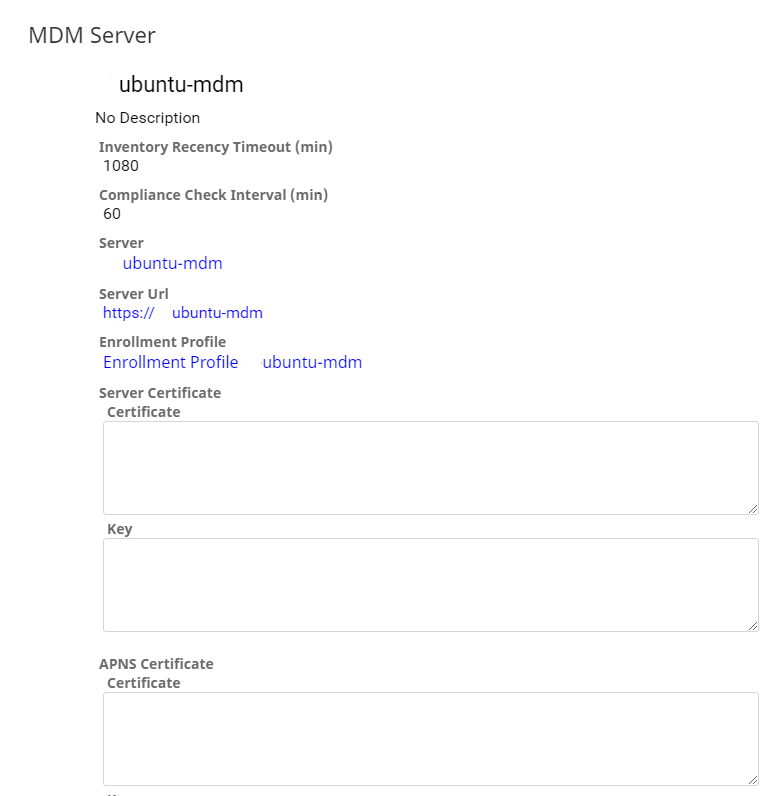
The next step is to configure the MDM Server, including the necessary certificates, and assign the enrollment Profile (created earlier) to your MDM Site Server.
Additional profiles can be created to configure for example Wifi, PPPC, Kernel Extension Policy or Restrictions.
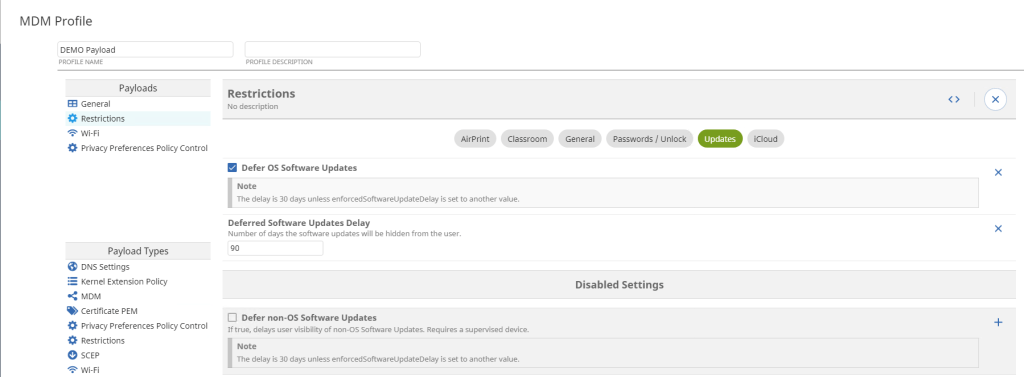

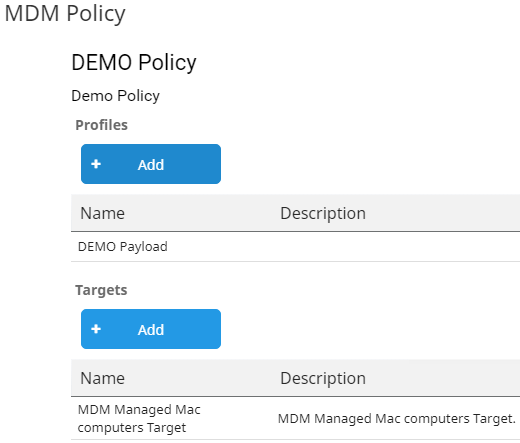
The created profiles (Demo Payload) can be assigned to a target (MDM Managed Mac computers Target)
In addition to profile creation you are able to use the right-click menu actions called MDM to trigger actions directly on the device. The following actions are available: „Inventory“, „Erase“, „Reboot“, „Shutdown“, „Lock Device“ and some Inventory Actions like: „All“, „Installed Profiles“ and „Security List“.

What to expect from the upcoming 8.6 RU2 release
ITMS 8.6 RU2 is expected to be released in Q1/2022 and currently the plan is to make the MacOS MDM functionality public available as part of the 8.6 RU2 Release.
The primary focus in ITMS 8.6 RU2 will be to improve the user experience (automating creation of Code Signing Request process) and to extend the functionality to support additional payload types.
There is a good chance that 8.6 RU2 will support the distribution of apps via MDM the import of profiles created in other products and possibly the automated enrollment through integration with Apple´s Device Enrollment Program (DEP).
My personal opinion (after the relase of 8.6 RU2): The next logical steps may be to extend the MDM capabilities to cover other Platforms like iOS, Windows 10/11 and possibly Android. With the introduction of MDM capabilities Symantec widely opens the possibilities for managing Platforms like iOS, Windows 10/11 and Android through MDM and makes the transition to a Unified Endpoint Management (UEM) Product .
For sure there will be other enhancements in ITMS 8.6 RU2 but this will be covered in a additional Blogpost. I´m super excited what this new enhancements would be. Stay tuned for this upcoming release.
PS: If you haven´t already registered for the upcoming EPM Virtual User Group Event on October 19th then register now to get an update on the current / latest status and ask questions.