
During my research on the Outlook Vulnerability CVE-2023-23397 my co-worker and college Martin created a Powershell script to update the vulnerable M365 versions with an Altiris Task to a version that wasn´t affected. A few hours later I discovered a proactive remediation script developed by Nicola Suter which does the same (same result).
What is Proactive Remediation?
Proactive Remediation is Microsoft´s way to do the same thing as Altiris does with software releases + a detection rule (if you want the short version…)
Proactive remediation scripts (mostly) consist of a detection and a remediation script. If the Exit Code of the detection script is 1 – the remediation script gets kicked off. If the Exit Code of the detection script is 0 – nothing happens – the remediation script doesn´t run.
In this Blogpost I want to show you how you can easily make use of proactive remediation scripts in Altiris ITMS instead of reinventing the wheel.
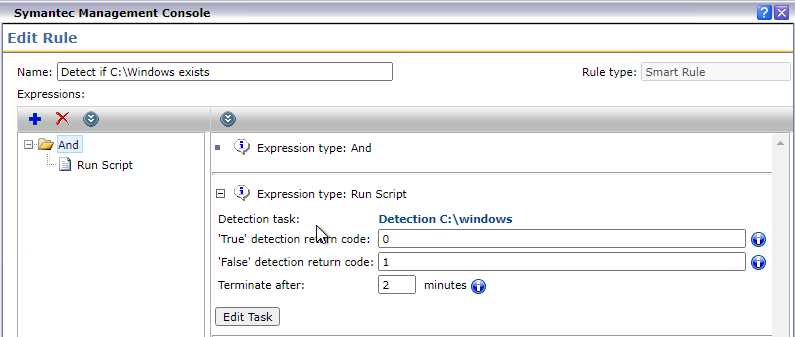
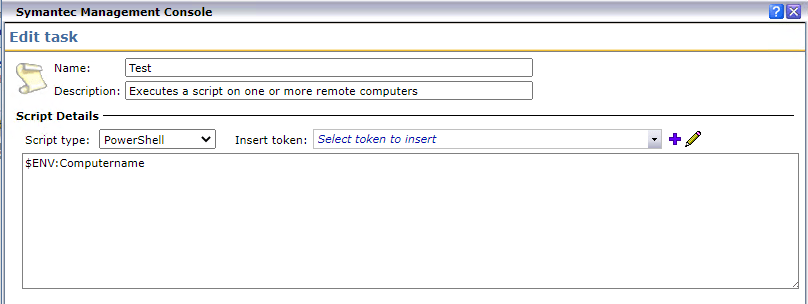
In Altiris proactive remediation scripts are the same as software releases with a run script detection rule. Since the release of ITMS 8.5 RU4 Symantec introduced the ability to allow a custom script to be used as detection rule. The Exit Codes can individually be defined, and they don´t have to be 0 or 1. You can define your own if you like.
Here is an example of a run script detection rule (I know that there is an easier method to check if C:\Windows exists but this is just to demonstrate how to use it)

In the Advanced Task options, you must specify “The task is succeeded if its return code is: 0,1“ or whatever Exit Codes you have specified in the script. Otherwise you will get the following error message: “Task success return code must include the specified values: 0,1”. Adjust “The task is succeeded definition in the advanced options of the task.


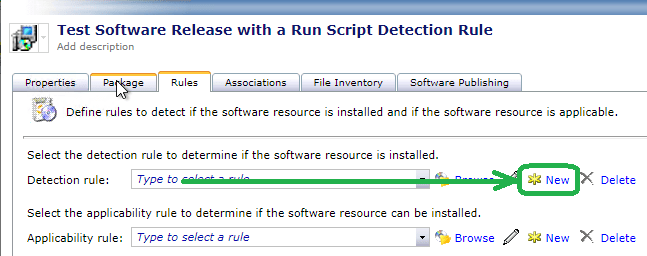
In ITMS version up to 8.6 RU3 the only way to create something almost identical as the proactive remediation scripts are to create a software release with a run script detection rule and then create a Managed Software Delivery Policy. Here is an example of how to create a software release with a run script detection rule:
ITMS 8.6 RU3 – create a software release with a run script detection rule


The key point is that until 8.7 got released, you could technically do the same like proactive remediation, but the remediation script has to be wrapped up as a Software release. From my point of view this wasn´t an issue but creating software releases is a little bit more time consuming than just using a Run Script Task in Altiris.
Proactive Remediation in ITMS 8.7
In the ITMS version 8.7 Symantec expanded the ability to use detection rules for Tasks. This means that you do not need to create a software release and apply a run script detection rule. It is far easier: You simply create a detection and remediation run script Task and then add the Task with the remediation script into a Managed Software Delivery Policy. In ITMS 8.7 you have a new option that allows you to specify to “run this Task only if the rule evaluates to True or False”.

The reason why I created this Blogpost is that this allows you to easily use Microsoft´s so-called proactive remediations in Altiris. Florian Salzmann, Joey Verlinden and Jannik Reinhard created a github repository with a collection of very useful proactive remediation scripts. So instead of creating everything from scratch you can now easily use the collection of proactive remediation scripts (or create your own) in Altiris. Most of them may be very useful for your environment.
Please keep in mind “sharing is caring”.
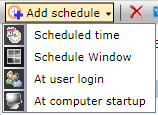
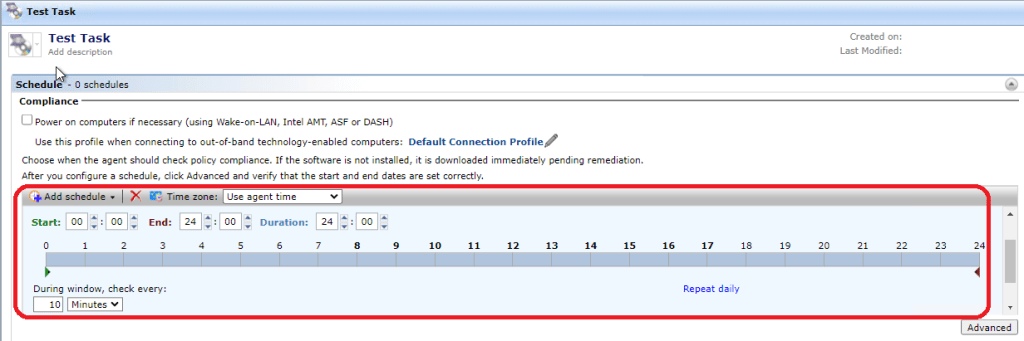
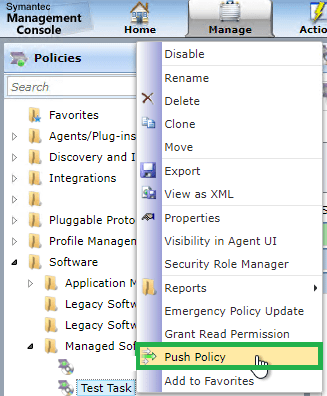
The scheduling options for Managed Software Delivery are much more granular to configure than the options in Intune… (it allows to get lower than 1 hour for the remediation…). You could also Push the Managed Software Delivery Policy immediately if needed when you have persistent connection configured and the policy is enabled. This allows you to respond immediately to security breaches like the CVE-2023-23397 (Outlook Vulnerability).
The Detection Rules are very powerful – beside the „Run Script“ detection rule there are many other options like Smart Rules and Standard Rules with the option to use a Operator like AND / OR. Please take a look at the Software Management Best Practices and Troubleshooting 8.5/8.6 guide. This is still valid for the ITMS 8.7 release.
If you have an idea for a script which is missing in the repository, please contact these guys or open an issue on the repository with a description of your idea. This will also help others to consume those scripts in Altiris or Microsoft Intune :).
Reference:
Software Management Best Practices and Troubleshooting 8.5/8.6
Jannik Reinhard / Twitter
Joey Verlinden / Twitter
Florian Salzmann / Twitter